The Best Strategy To Use For Risk Management Enterprise
Table of ContentsOur Risk Management Enterprise IdeasThe Only Guide for Risk Management EnterpriseThe Greatest Guide To Risk Management EnterpriseThe Best Strategy To Use For Risk Management EnterpriseThe smart Trick of Risk Management Enterprise That Nobody is Talking AboutRisk Management Enterprise Fundamentals ExplainedGet This Report about Risk Management Enterprise
Below are several of its crucial functions that facilities must recognize. So, have a look. Real-Time Risk Evaluations and Mitigation in this software permit companies to continuously monitor and evaluate dangers as they progress. This attribute leverages real-time information and automated evaluation to determine potential risks without delay. When risks are identified, the software promotes instant reduction actions.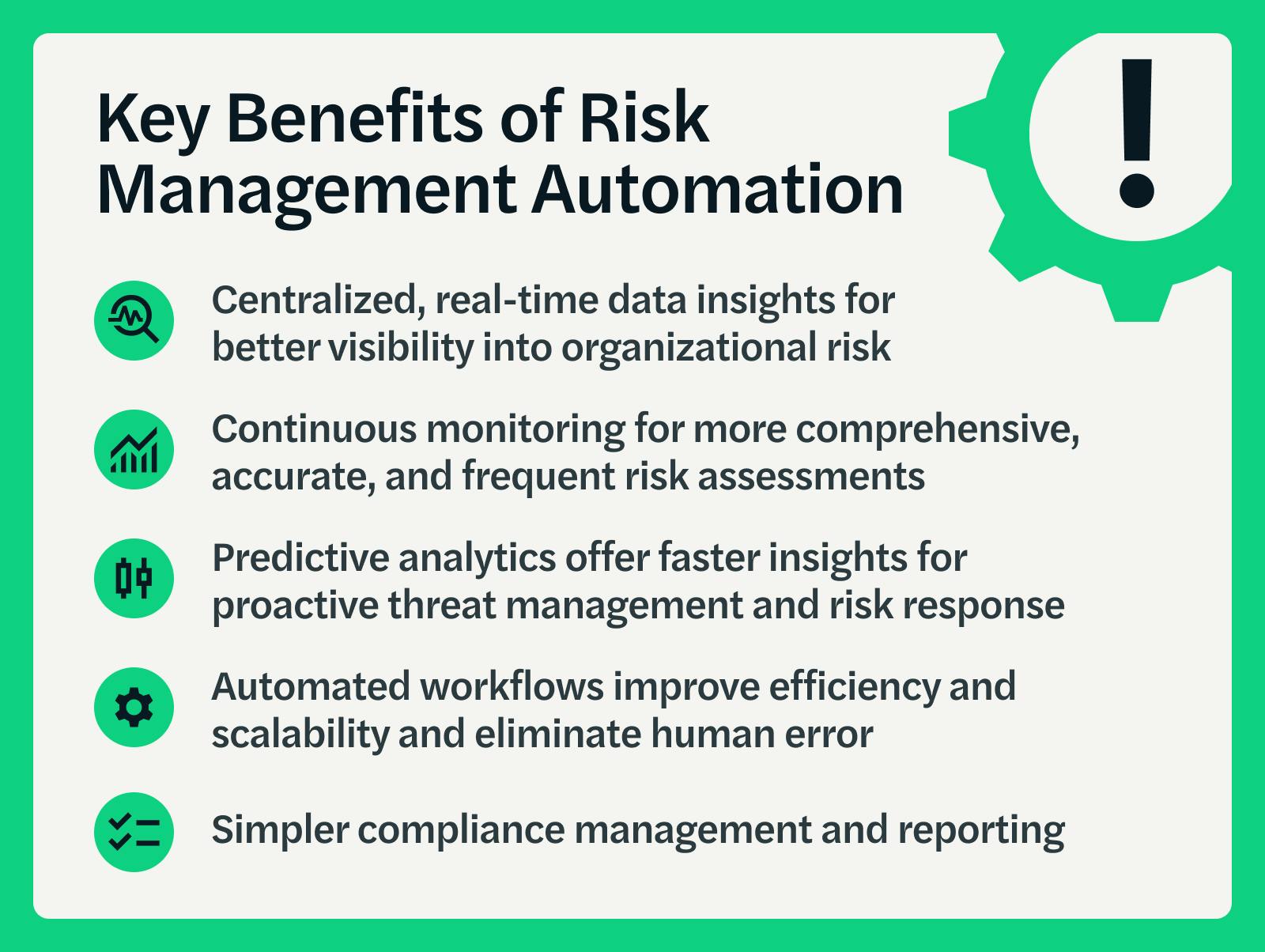
They address the difficulty of continuous threat management by offering devices to keep an eye on risks continuously. KRIs boost protection risk oversight, making sure that possible risks are identified and handled successfully.
An Unbiased View of Risk Management Enterprise
IT take the chance of monitoring is a part of venture danger administration (ERM), developed to bring IT run the risk of according to an organization's risk cravings. IT take the chance of monitoring (ITRM) includes the policies, treatments and technology necessary to reduce hazards and susceptabilities, while preserving compliance with applicable governing demands. Additionally, ITRM seeks to restrict the repercussions of damaging occasions, such as safety breaches.
Veronica Rose, ISACA board director and an information systems auditor at Metropol Corp. The ISACA Threat IT framework straightens well with the COBIT 2019 framework, Rose claimed.
Business Danger Monitoring Software Advancement: Perks & Qualities, Cost. With technological improvements, threats are continually on the rise., companies browse via a constantly altering sea of dangers.
About Risk Management Enterprise
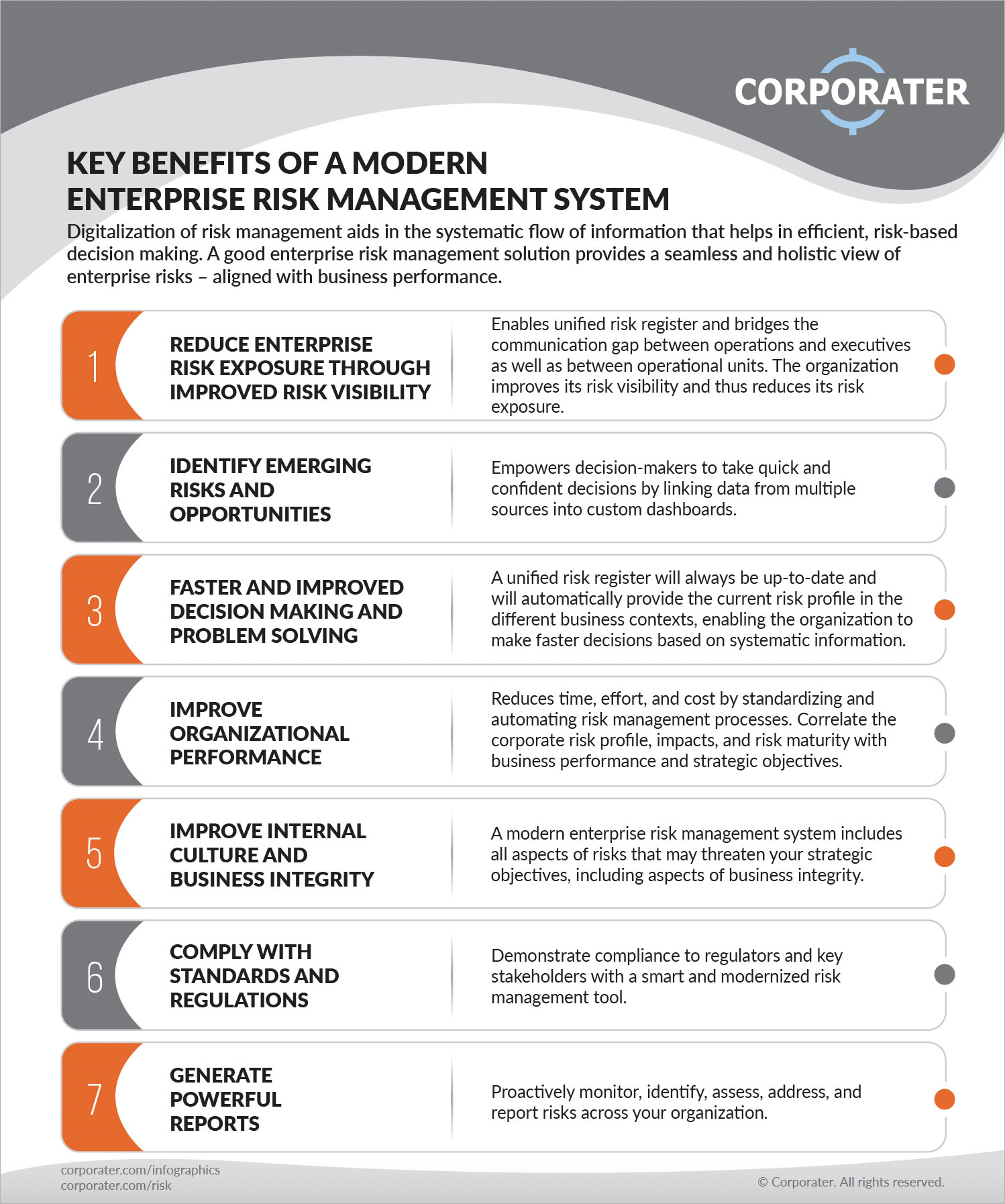
In this blog site, we will certainly dive right into the world of ERM software application, exploring what it is, its benefits, attributes, and so on to ensure that you can develop one for your organization. Venture Threat Administration (ERM) software application is the application program for planning, routing, arranging, and managing company activities and simplifying danger administration processes.
With ERM, companies can make insightful decisions to boost the general strength of the company. Committed ERM systems are important for businesses that on a regular basis deal with vast quantities of sensitive info and several stakeholders to approve tactical choices.
It can be stayed clear of by using the ERM software application system. This system automates guideline conformity monitoring to keep the organization protected and certified.
All about Risk Management Enterprise
You can likewise link existing software application systems to the ERM by means of APIs or by adding data by hand. Organizations can make use of ERM to review dangers based on their prospective impact for better threat monitoring and mitigation.: Including this function allows customers to obtain real-time notices on their devices concerning any kind of danger that might occur and its influence.

Rather, the software allows them to set thresholds for different processes and send out press alerts in instance of feasible threats.: By incorporating information visualization and reporting in the custom ERM software, companies can acquire clear insights regarding threat trends and performance.: It is obligatory for companies to stick to market compliance and regulative requirements.

These systems make it possible for companies to carry out best-practice danger management processes that align with sector criteria, using a powerful, technology-driven method to identifying, assessing, and mitigating threats. This blog site checks out the benefits of automated threat administration tools, the locations of threat administration they can automate, and the value they bring to a company.
Facts About Risk Management Enterprise Uncovered
Groups can establish up forms with the pertinent fields and conveniently produce different forms for various risk kinds. These danger analysis forms can be flowed for completion using automated workflows that send out notices to the pertinent personnel to finish the forms online. If types are not completed by the due date, after that chaser emails are immediately sent by the system.
The control tracking and control screening process can likewise be automated. Companies can utilize computerized workflows to send out normal control test notifications and team can enter the results using on the internet forms. Controls can likewise be checked by the software by setting regulations to send notifies based upon control information kept in other systems and spread sheets that is drawn right into the system via API combinations.
Threat management automation software application can likewise sustain with danger coverage for all degrees of the venture. Leaders can view reports on danger direct exposure and control performance via a selection of reporting outputs including static reports, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The capability to pull actual time records at the touch of a switch reduces out strenuous information manipulation tasks leaving risk groups with even more time to assess the information and advise business on the very best strategy.
The requirement for find out efficient has actually never ever been a lot more pressing. Risk Management Enterprise. Organizations operating in competitive, fast-changing markets can not pay for delays or inefficiencies in dealing with potential dangers. Standard danger management utilizing hand-operated spreadsheet-based procedures, while familiar, frequently bring about fragmented information, taxing coverage, and an increased likelihood of human error. Automating the danger administration procedure with software program addresses these imperfections.
The Buzz on Risk Management Enterprise
This makes certain risk signs up are constantly current and lined up with business objectives. Compliance is an additional crucial motorist for automating risk administration. Requirements like ISO 31000, CPS 230 and COSO all provide support around threat management best methods and control structures, and automated threat management devices are structured to line up with these needs assisting companies to fulfill most commonly utilized danger administration criteria.
Look for risk software platforms with an authorizations power structure to conveniently set up workflows for threat rise. This functionality allows you to tailor the view for each and every individual, so they only see the data appropriate to them. Make certain the ERM software program supplies customer monitoring so you can see that entered what information and when.
Look for out devices that supply task risk monitoring capacities to manage your projects and profiles and the connected risks. The benefits of embracing threat monitoring automation software expand far past effectiveness.
The 5-Second Trick For Risk Management Enterprise
While the case for automation is engaging, carrying out a risk monitoring platform is not without its challenges. For one, information quality is important. Automated systems rely upon accurate, up-to-date details to provide meaningful understandings. To overcome the obstacles of risk monitoring automation, organizations have to purchase information cleansing and administration to guarantee a strong foundation for executing an automated system.
Automation in danger monitoring empowers companies to change their strategy to risk and develop a more powerful foundation for the future (Risk Management Enterprise). The question is no much longer whether to automate threat management, it's how soon you can start. To see the Riskonnect in activity,
The answer typically exists in just how well risks are anticipated and handled. Job monitoring software program works as the navigator in the tumultuous waters of job execution, offering devices that determine and analyze threats and devise strategies to reduce them successfully. From real-time information analytics to detailed threat surveillance control panels, these devices give a 360-degree sight of the task landscape, making it possible for task supervisors to make educated decisions that maintain their jobs on track and within budget.